The Coronavirus epidemic has claimed nearly 3200 lives and infected more than 93,000 people across the globe and the numbers continue to rise every day. As health officials struggle to contain the COVID-19 and disseminate accurate information, some app developers are taking advantage of the situation to launch adware-ridden apps.
Coronavirus apps are bad news
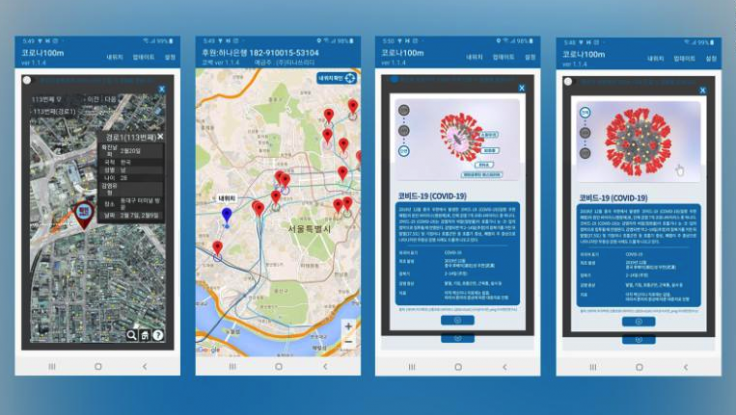
Over the last week, coronavirus-tracking apps have been popping up on the Google Play Store. While these apps promise to keep you updated with all the latest information about the Coronavirus outbreak in order to help keep you safe and prevent the spread of the disease, they have an ulterior motive: to install adware on your device, as pointed out by WRCB-TV.

For instance, the Corona Tracker app, although free to download, is laced with ads and that's how the app developer intends to monetise the platform. Every page visit triggers an ad. While it does have a map that and supposed latest figures, the statistics were found to be inaccurate by hundreds thanks to a similar tracker run by reputable source Johns Hopkins University.
How do these apps make money?
The app continues to run ads, sometimes even in the background, with the intention to generate ad revenue for the developer and drain your phone's battery. You can lose as much as six percent of battery even if you use the app for less than two minutes.
The scary-looking Coronavirus app is also guilty of abusing the epidemic and make money off of it by running ads. The app, which only shows the history of the virus, is also free but you can pay $2 to remove the ads or make a donation of up to $100 to the developer.
There are at least a dozen similar coronavirus-related apps on Google's app marketplace. Apple, on the other hand, has blocked them from its App Store except for one app from Brazil.
Coronavirus malware
Last month, we reported that there has been a spike in the number of websites with domain names related to the deadly virus. Security researchers found these sites to be dangerous as their main objective was to distribute Trojan malware and conduct phishing activities.
In this case, the Trojan works by posing as a disability welfare service provider and reporting where the virus has spread in Japan. It also points the malware victims to a malicious email attachment, which will allow the malware to be downloaded if they open it.









