While the world deals with a global virus outbreak, you also need to be vigilant about viruses that can infect your mobile devices. Security researchers have uncovered a host of utility and children's Android apps that are laced with a dangerous new strain of malware.
Which Android apps are carrying malware?
Researchers at security firm Check Point discovered that several popular utility and kids' apps on Google's Play Store with more than a million installs contain malware that farms ad clicks to earn money.
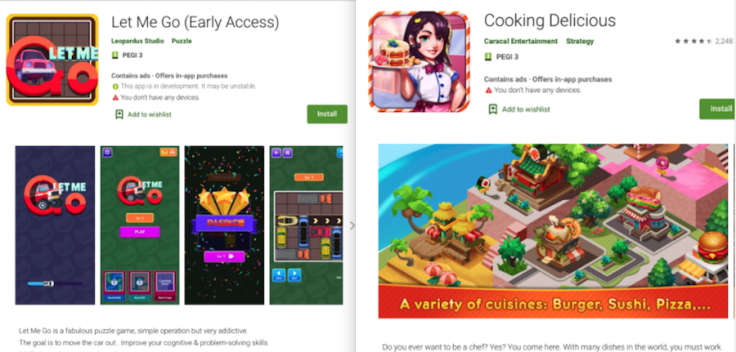
The new malware, dubbed, Tekya, was found in 56 apps in total, out of which 24 of them were apps for kids (ranging from puzzle apps to games), while the rest were utility apps such as recipe apps, calculators, weather apps, translators among others. The apps have since been removed from Google's app marketplace after Check Point disclosed its findings to the company.
The full list of affected apps has been revealed by Check Point in its security report. If you've previously installed any of the infected apps, it is strongly recommended that you uninstall them immediately, and make sure you've updated your device with the latest security patches and operating system version. Additionally, you can also invest in some sort of mobile security software to prevent exposing your smartphone to malware in the future.
Last month, Google announced in a blog post that it removed 790,000 malicious apps from the Play Store. It also noted its Google Play Protect software had prevented more than 1.9 billion malware installations from non-Google Play sources in 2019. However, despite these measures, the app marketplace often fails to detect malware-ridden apps.
How does Tekya operate?
The malware imitates user actions to automatically click ads and banners without the user's knowledge to generate ads from networks Google's AdMob, AppLovin', Facebook, and Unity, in a bid to earn revenue by committing ad fraud. What makes this malware dangerous is its ability to bypass Google and the Play Store's security protocols, as pointed out by Check Point.
"To us, the amount of applications targeted and the sheer number of downloads that the actor successfully infiltrated into Google Play is staggering," Aviran Hazum, manager of mobile research at Check Point, said.
"Combine that with a relatively simple infection methodology, [and] it all sums up to the learning that Google Play Store can still host malicious apps. It is difficult to check if every single application is safe on the Play Store, so users cannot rely on Google Play's security measures alone to ensure their devices are protected," he added.









