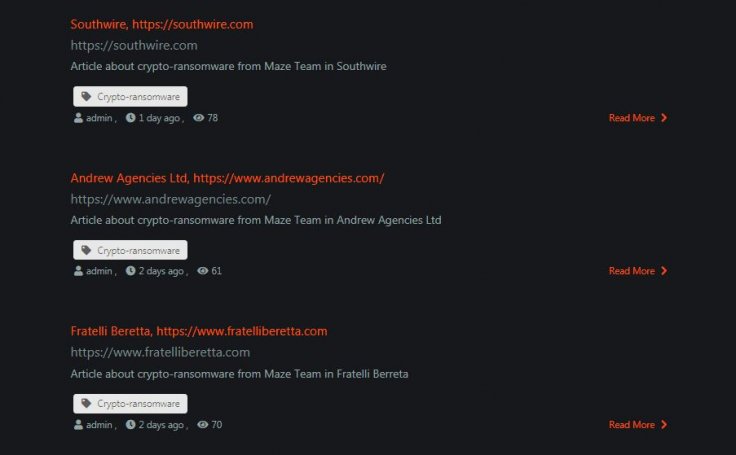
Targeted ransomware attacks are getting more famous for their abilities to launch disruptive and destructive attacks against the enterprises. And since 2019, Maze has become a known entity in the world of ransomware. Starting May 2019, cybercriminals are actively using Maze Ransomware to breach victims data and publish on a public-facing site to extract extortion money.
The latest two additions to its victim's list are two American enterprises. Out of the two, one is a wire manufacturing company named Southeastern Wire, and another is an injection moulded plastic component manufacturer Koller Craft LLC.
Following their attacking fashion, they have reportedly stolen millions of data records from the compromised servers, lock the entire computer system network and inform the authorities to meet the asked ransom. In both cases, the ransomware operators have managed to steal a massive amount of sensitive data from both the enterprises and leaked a bit of it to compel the Enterprises to meet their demand.
The Data Leak
From the Southwestern Wire hack, the threat actors have leaked 20 GB worth sensitive data, and an undisclosed amount of data from the Koller Craft LLC. Cybersecurity solution provider Cyble has scrutinised the Southwestern Wire data leak and confirmed that it consists of highly sensitive corporate data such as payroll, production data, tax-related documents and many more.
Ransomware attacks are skyrocketing
After a surprising plunge in 2019, ransomware attacks have skyrocketed starting the beginning of this year. Attacks on healthcare services, pharmaceutical labs, government authorities, universities and large enterprises are prevalently increasing this year. And the actors behind the Maze Ransomware are playing an essential role in the game.
The Cognizant attack
Last month they compromised one of the largest IT service provider Cognizant impacting around $50 to $70 million worth loss. Cognizant Chief Financial Officer, Karen McLoughlin in an earnings call has mentioned the amount would increase further due not-yet-known legal, consulting, and other costs associated with the investigation, service restoration, and remediation of the breach.
The City of Pensacola Attack
The Maze Ransomware Operators was behind the infamous City of Pensacola attack. In the attack, the operators encrypted the entire data and demanded $1 million for decrypting the data. The operators were, however, mentioned later that they had no strings attached with the terrorist attack at Naval Air Station (NAS) Pensacola happened just days before the ransomware attack.
The Maze Ransomware utilises Exploit Kits, Remote Desktop connections with lame passwords and email phishing to get into the victim's systems. It utilizes RSA and ChaCha20 encryption methods to encrypt the victim's data.









