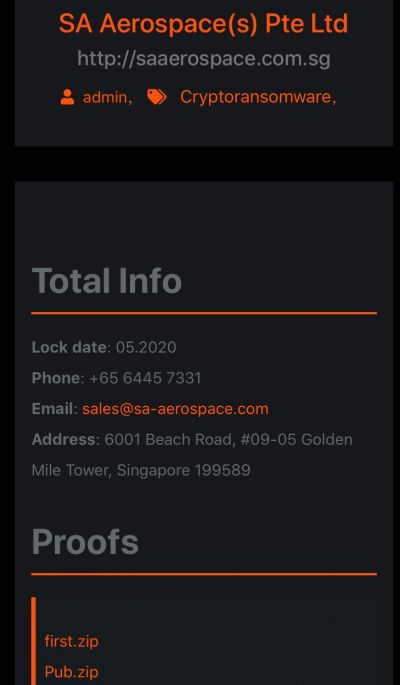
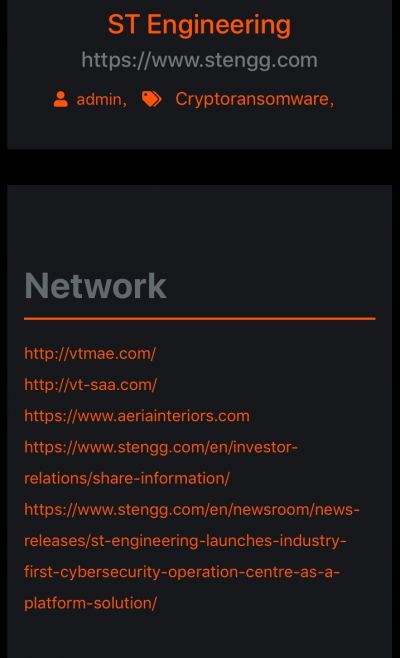
VT San Antonio Aerospace (VTSAA), a U.S. subsidiary of Singapore's ST Engineering Aerospace, was hit by a ransomware attack in March. About 1.5 terabytes worth sensitive data was encrypted and later leaked by a hacker group Maze, affecting the U.S. operations of the company.
Before launching the ransomware attack and encrypt the systems, Maze stole data of VTSAA's contract agreements with various governments and government organizations including NASA and American Airlines. Among countries, the data includes the government contracts of Peru, Argentina among others. Maze had access to financial records beside projects, equipment and schedules of such.
VTSAA Vice President, Ed Onwe, confirmed that the hacker group had access to their network and the threat had been contained. "At this point, our ongoing investigation indicates that the threat has been contained and we believe it to be isolated to a limited number of ST Engineering's US commercial operations. Currently, our business continues to be operational," Onwe said in a statement.
The company has about 23,000 employees with a revenue of around $8 billion. It has undertaken various smart city projects in 130 cities across the globe and has defense, government and commercial contracts with over 100 countries.
How the network was breached
Despite leaking several financial spreadsheets and other details on their lean site, Maze didn't describe how they gained access to VTSAA's network. However, it is believed, Maze connected to the company's servers through a remote desktop connection using a compromised administrator account, gaining access to the domain administrator. Eventually, they had access to VTSAA's domain controllers, file servers on two domains and intranet servers.
VTSAA, however, managed to regain access and recover data within three days of the attack. "Upon discovering the incident, the company took immediate action, including disconnecting certain systems from the network, retaining leading third-party forensic advisors to help investigate and notifying appropriate law enforcement authorities," said Onwe.
"As part of this process, we are conducting a rigorous review of the incident and our systems to ensure that the data we are entrusted with remains safe and secure. This includes deploying advanced tools to remediate the intrusion and to restore systems. We are also taking steps to further strengthen the Company's overall cybersecurity architecture," he added in the statement.

Maze Attack on U.S. Nuclear Missile Contractor
The attack on VTSAA was not an isolated one, though. On June 4, it was also revealed that Maze had access launched a similar attack on the networks of Westech International, a U.S. defense contractor which maintains the Minuteman III intercontinental ballistic nuclear-missile program.
In a similar move, Maze started leaking sensitive documents to extort the company in paying a ransom. Later, they encrypted the system.
"Upon learning of the issue, we immediately commenced an investigation and contained our systems. We have also been working closely with an independent computer forensic firm to analyze our systems for any compromise and to determine if any personal information is at risk," Westech said in a statement.
In April, Maze also hacked IT services giant Cognizant Solutions systems, causing temporary disruption of its services. The other incidents include Allied Systems and City of Pensacola, Florida, U.S. among others.









