A security researcher from the Dutch university Eindhoven University of Technology called Björn Ruytenberg has revealed a minacious vulnerability in all non-macOS running computers with a Thunderbolt port. This means any laptop or personal computer having a Thunderbolt port and running on Windows or other distros of Linux is vulnerable to the attack. The researcher claims the port can compromise your device data even if it gets encrypted.
How Thunderspy works
According to Ruytenberg, the attack doesn't require any phishing attack or loading a malicious link on the victim's device. The Thunderspy attacks can be executed even if the target device has Secure Boot, strong BIOS and operating system account passwords, as well as full disk encryption. All that the attacker would need was to gain physical possession of the device for just a few minutes.
Thunderspy targets
The attack targets all Intel-designed Thunderbolt ports shipped after 2011. Ruytenberg has found seven vulnerabilities in Intel's Thunderbolt design and came up with nine real-life scenarios to prove the concept.
Windows operating system and Surface hybrid laptop developer Microsoft is reportedly well aware of the direct memory access (DMA) vulnerabilities in the Intel designed Thunderbolt 3 ports, prompting them to sacrifice the Thunderbolt ports in all the latest Surface devices.
Ruytenberg explained that the ThunderBolt port, which is a PCIe device, comes with DMA which could help an attacker to control the system memory through a connected accessory. The Thunderbolt technology could get executed at the operating system level with kernel-level DMA access protection. But this technology is available only in laptops rolled out since 2019.
Microsoft has already rolled out kernel DMA protection against all sorts of physical attack via Thunderbolt 3 connected PCI devices. The update has been rolled out with Windows version 1803 for most of its OEM partners like Dell, Lenovo, HP and Acer which have adopted Thunderbolt 3 ports.
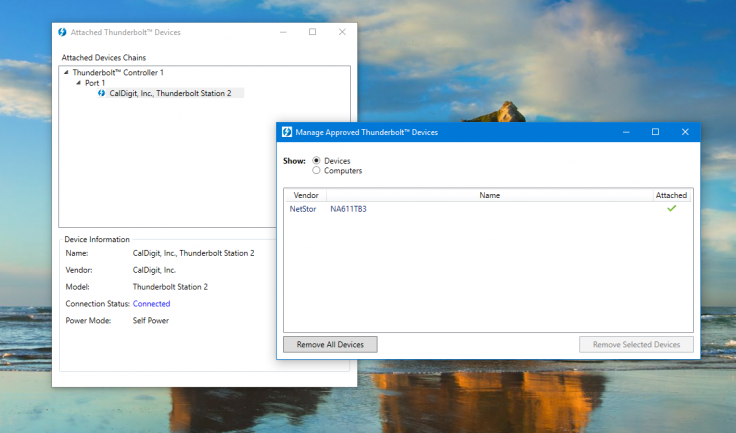
Intel has also unleashed a policy management feature dubbed Security Levels to allow system administrators to adopt cryptographic authentication for available PCIe connections.
Incapable patches
Ruytenberg has mentioned that his discovery Thunderspy could destroy all Intel-adopted security levels by exploiting mediocre firmware verification, improper firmware authentication and inauthentic controller configurations, SPI flash interface deficiencies and so on.










