Researchers at Awake Security, an advanced network traffic analysis company, said that a newly found spyware effort attacked users through 32 million downloads of extensions to Google's Chrome web browser. As per the experts, it has highlighted the tech industry's failure to protect browsers as they are used more for email, payroll, and other sensitive functions.
The tech giant Google said after the researchers alerted the officials, it has removed over 70 of the malicious add-ons from its official Chrome Web Store. A spokesman of the company Scott Westover said that after they received the alert about the extensions in the Web Store that violate Google's policies, "we take action and use those incidents as training material to improve our automated and manual analyses."
Most of the free extensions purported to warn Chrome users about questionable websites or convert files from one format to another. Instead, they drew off browsing history and data that provided credentials for access to internal business tools. The Awake co-founder and chief scientist Gary Golomb explained that depending on the number of downloads, it was the most far-reaching malicious Chrome store campaign identified as of now.
The Spyware Campaign
As per tech experts, spyware is unwanted software that infiltrates user's computers, steals internet usage data, and sensitive information. This malicious campaign is classified as a type of malware — malicious software designed to gain access to or damage a user's computer, often without the knowledge of the user.
In the recent case, Alphabet Inc's Google did not explain how the new spyware compared with previous malicious campaigns, the breadth of the damage, or why it did not detect and remove the bad extensions on its own despite past promises to supervise offerings more closely. It is also not clear who was behind this operation, while the researchers at Awake revealed that the developers supplied fake contact information when they submitted the extensions to Google.
Former National Security Agency engineer Ben Johnson, who founded security companies Carbon Black and Obsidian Security told Reuters that "Anything that gets you into somebody's browser or email or other sensitive areas would be a target for national espionage as well as organized crime."
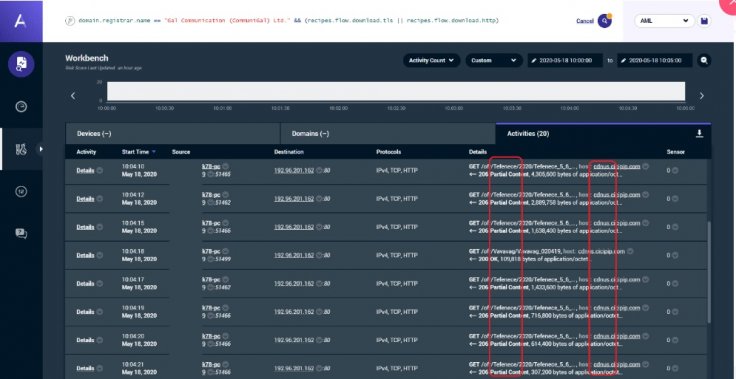
In addition, Golomb said that the extensions were designed to avoid detection by antivirus companies or security software that evaluates the reputations of the web domains. The researchers noted that if someone used the browser to surf the web on a home computer, it would connect to several websites and transmit information.
In terms of the corporate network, which includes security services, it would not transmit sensitive information or reach the malicious versions of the websites. As per Golomb, it showed that "how attackers can use extremely simple methods to hide, in this case, thousands of malicious domains."

Domains in Question
As per the report, all these domains, over 15,000 linked to each other in total, were purchased from an Israel based registrar, Galcomm, known as CommuniGal Communication Ltd. The researchers said Galcomm should have known what was happening.
In response, the owner of Galcomm, Moshe Fogel said the company is not involved, and not in complicity with any malicious activity whatsoever. He also added that "You can say exactly the opposite, we cooperate with law enforcement and security bodies to prevent as much as we can." Fogel explained that there was no record of the inquiries Golomb said he made in April and in May to the company's email address for reporting abusive behavior, and he asked for a list of suspect domains.
Malicious activities have emerged as a global issue in recent times. The developers of such campaigns have been using Google's Chrome Store as a conduit for a long time. In 2018, after one in 10 submissions was deemed malicious, Google said it would improve security measures, in part by increasing human review. But in February 2020, independent researcher Jamila Kaya and Cisco Systems' Duo Security uncovered a similar Chrome campaign that stole data from nearly two million users. Google joined the investigation and found 500 fraudulent extensions.









