An unknown cyber group from eastern Europe has stolen $70 million from Israel cryptocurrency exchanges, revealed cyber-security company ClearSky. The report said the crypto cyber gang, dubbed as "CryptoCore," has robbed cryptocurrency exchanges worth $200 million, especially focusing on Japan and the U.S.
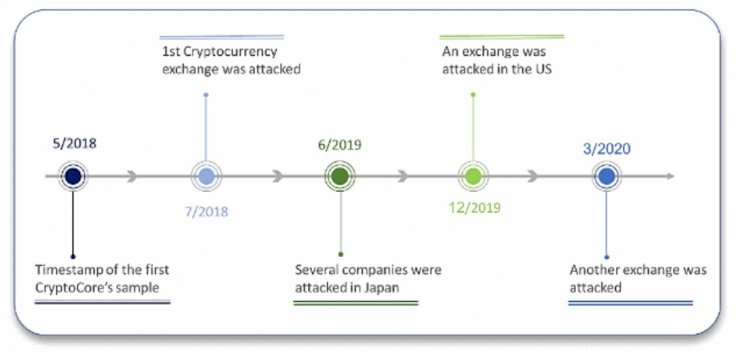
As per the report, the ClearSky has been tracking the CryptoCore group campaigns for almost two years, with no conclusive understanding of the operators' origin. However, the company assessed with a medium level of certainty that the group has links to the East European region, Ukraine or Russia.
Or Blatt, Research Team Leader at ClearSky said they linked CryptoCore to five successful hacks and have noticed the group to target another 10 to 20 cryptocurrency exchanges. Some of the operations by the threat actors have been previously documented in several reports identifying the group as "Dangerous Password" and "Leery Turtle [PDF]."
But as per the Israeli security firm, CryptoCore's operations have been more ample and widespread than previously documented. In the report, the security firm clarified that,
Cryptocurrency exchanges have become targets for constant attacks... Threat actors of all kinds try to infiltrate corporate networks for reconnaissance, ransomware deployment, and plainly to steal money from those exchanges, specifically from their 'hot' (i.e. active, connected) wallets

The Tactics Are Same
As per the ClearSky despite operating for almost two years, the attacking tactics are almost the same, with a little variation. All attacks start with an information gathering stage during which the cybercriminals collect the required information to target an exchange's management, IT staff, and other employees.
They usually launch the first phishing attacks against personal email accounts, rather than the corporate ones, as they are less secure. ClearSky said that it is just a matter of hours to weeks until the spear-phishing email is sent to a corporate email account of an exchange's executive. The attacks are typically carried out by impersonating a high-ranking staff either from the target organization or from another organization with connections to the targeted employee.
The ultimate goal is to plant malware on an employee's system and gain access to a password manager account. The hackers from CryptoCore will use those passwords to access accounts and wallets, disable two-factor authentication systems, and then start transferring funds out of the exchange's "hot wallets."
While North Korea bases hackers have been the biggest threat to the cryptocurrency exchanges, CryptoCore is now the second group that has repeatedly targeted cryptocurrency exchanges during the past three to four years. However, the United Nation's panel on threat intelligence released a report which said that North Korean hackers stole around $571 million from at least five cryptocurrency exchanges in Asia between January 2017 and September 2018.









