Microsoft Windows, the most used operating system in the world, is also the most popular among hackers for its security vulnerabilities. In the last two weeks alone there have been reports of two security risks that can be exploited to plant malware and ransomware. Now, even the seemingly most harmless custom themes are a security risk that can be exploited to steal Windows password.
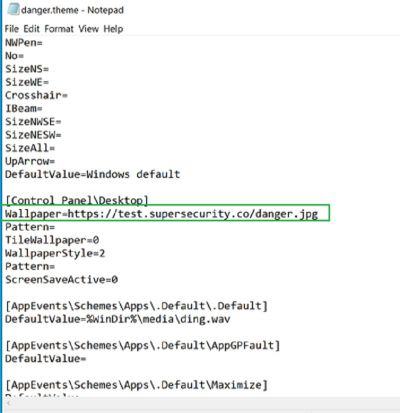
A user can customize Windows themes changing the accent color, wallpaper cursors and sounds. While doing that, a theme's setting is then gets saved in AppData with a '.theme' extension. The user can then share the theme by saving it in the desired folder from the Windows settings option. The theme package is saved with a '.deskthemepack' extension that can be shared through a mail attachment.

Pass-The-Hash Attack
All a hacker needs to do is weaponize the theme pack. With a few tricks and steps, a hacker can craft a theme pack that can be used to conduct a pass-the-hash attack or in simple terms to steal your Windows login name password.
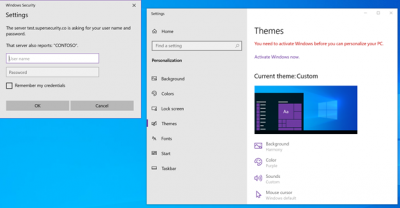
In such attacks, when you try to install the theme pack, you will be prompted to give your Windows administrative username and password. The trick is that it is a remote SMB (server message block) that requires authentication. Windows will automatically try to access the remote server by sending the username and password in New Technology Lan Manager (NTLM) hash, security researcher Jimmy Bayne revealed.
The problem is that Windows is now actively asking users to log in with their Microsoft accounts (Hotmail, Live, Outlook, etc) and those credentials also get stored during the attack. The hacker then uses those harvested login credentials to dehash the password which takes only a few seconds for easy sounding ones. The attacker then can access the computer of the user, who downloaded the theme, to steal files and even access Microsoft accounts that also include its cloud services (Azure).
"These gimmicky themes are clearly not created with security in mind, and at the risk of exposing passwords and other sensitive data, I would suggest users think twice when installing them," Jake Moore, ESET's cybersecurity specialist told Forbes.
How to Protect Your PC?
The easiest way to protect your computer is to not download any custom theme from dubious sources. Microsoft told Bayne that the vulnerability wouldn't be fixed as it is a "feature by design." The other method you can use is to configure your group policy.
After opening the Group Policy editor by either typing gpedit.msc in Run or searching settings option for the feature, a window will open. There, a user can create a policy with the name "Network security: Restrict NTLM: Outgoing NTLM traffic to remote servers". Then, set all permissions to "Deny All" and it will stop sending the NTLM credentials, BleepingComputer reported.









