Despite recent security improvements, Android devices are still vulnerable to cyber attacks. Tech giant, Microsoft, has recently detected a new strain of malware that has been infecting Android devices. The malware, which comes bundled with malicious apps from third-party app stores and forums blocks access to the phone by showing a ransom note.
Ransomware attacks abusing Android's accessibility feature isn't uncommon. Hackers have often abused Android's "SYSTEM_ALERT_WINDOW" to encrypt mobile devices the same way as computers and demand a ransom. As cybersecurity researchers started notifying Google about the potential exploit, Android 10 came up with stronger protection against such attacks. But it hasn't stopped.
Abusing Notification Access
But the new malware, dubbed as AndroidOS/MalLocker.B is unique. The malware that Microsoft noticed doesn't encrypt the device completely unlike a ransomware attack on computers. Instead, it abuses Android's notification access to display an overlay screen. It blocks access to any other application on the device. Even restarting the device won't bypass the window.

Microsoft believes hackers have developed a novel technique. By combining the mechanism behind SYSTEM_ALERT_WINDOW and call notifications, a display overlay with the ransom note will be shown. For example, incoming call notifications require users' immediate attention and the mechanism behind it has been abused by hackers.
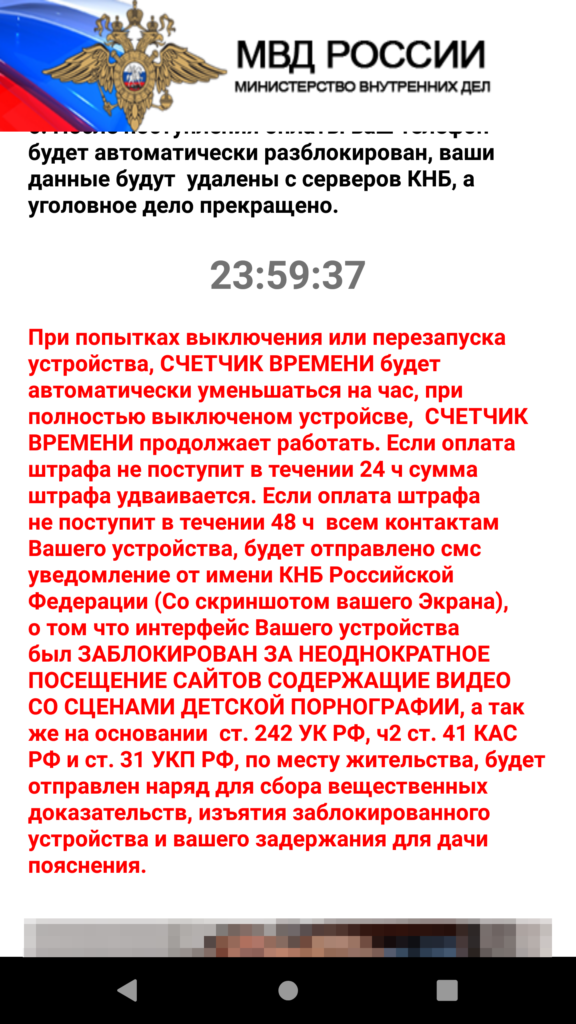
While if a user presses the "home" button, the activity goes to the background, in this case, the overlay screen cannot be bypassed. "The malware connects the dots and uses these two components to create a special type of notification that triggers the ransom screen via the callback," Microsoft said in the blog. It also shared a ransom note that was displayed on an Android phone user in Russia. It mimicked Russian police authority.
For the new ransomware attacks, hackers use explicit images from the device or fake police fines for the display overlay. By doing so, it can make the user believe and force the user to pay a ransom. In addition, the malware also uses a machine-learning algorithm. As many Android devices come in different screen sizes, the malware sample Microsoft investigated, could automatically adjust to the screen using machine learning algorithms. That way, it can ensure that the ransom note is displayed properly.
"This particular threat family has existed for a while, and it has used many techniques to compromise the user, but what we saw here is that it was not doing what we expected or what it was doing in the past," Tanmay Ganacharya, who leads the Microsoft Defender's threat research team, told the Wired.
Download Apps Only from Play Store
Similar to computer malware, MalLocker.B comes bundled with popular video players or games but they are actually fake versions of the apps that have been manipulated with malicious codes. Microsoft said that such apps are mostly found on untrusted sources such as third-party app stores or forums and advised only to download from the official Google Play Store.
According to Ganacharya, MalLocker.B is an evolved version of a similar malware family. With stronger protection for Android, the malware has been tweaked to meet the requirements. "This particular threat family has existed for a while, and it has used many techniques to compromise the user, but what we saw here is that it was not doing what we expected or what it was doing in the past," Ganacharya added.









