Cyberattack generally does not lead to death unless it is from the script of popular TV series Mr Robot. However, in a first of its kind, a patient at a German hospital died due to a ransomware attack on September 10.
The patient, who needed urgent medical attention, was taken to University Clinic Dusseldorf but had to be diverted to a distant facility — around 30 kilometers (18.6 miles) away — as the systems were down due to a ransomware attack.
The patient, identified as only a woman, died shortly after being rerouted to a hospital in Wuppertal. The hospital had to shut outpatient treatments and emergency care due to the attack saying that the hackers exploited a "widely used commercial add-on software."
Ransomware Attack
From September 10, the hospital networks were down with 30 servers encrypted following the cyberattack that crippled its networks. The hackers exploited a security vulnerability in Citrix Application Delivery Controller (NetScaler ADC), a network software, to gain access to the hospital systems and encrypted the servers. While the attackers left a note in one of the servers, they didn't mention any amount as ransom.

The vulnerability, known as CVE-2019-19781, was first identified in December 2019 and since then it has been exploited multiple times. The exploit allows hackers to create a reverse shell and full access to the victim's internal networks without any authorization. Experts at Positive Technology determined that over 80,000 companies across the world were at risk of being hacked.
"This vulnerability allows any unauthorized attacker to not only access published applications but also attack other resources of the company's internal network from the Citrix server, Positive Technologies said in a blog post. The company's security researcher, Dmitry Serebryannikov first discovered the vulnerability.
Citrix released a fix in January 2020 for the vulnerability and urged its customers to patch the systems. However, many firms are yet to apply the patch.
"We warned of the vulnerability back in January and pointed out the consequences of its exploitation. Attackers gain access to internal networks and systems and can paralyze them months later. I can only urge you not to ignore or postpone such warnings but to take appropriate action immediately," said Arne Schonbohm, President of Bundesamt für Sicherheit in der Informationstechnik (BSI), Germany's cybersecurity agency.

'Mistakenly Hacked'
However, the target of the hack was not the hospital and the note left in the server to contact them and it addressed Heinrich Heine University. The hospital was affiliated with the university. The Dusseldorf police contacted the hackers and informed them that they had encrypted the hospital system and not the university, endangering patients.
The hackers then withdrew the attack and provided with a decryption key to get the systems back online. As per Germany's justice department, the attackers could not be reached anymore, reported German news outlet NTV.
The hospital said that no data was stolen or deleted during the attack and it was recovering the systems. But the data recovery process is expected to be slow even after provided with the decryption key. "Due to the size of the IT system and the abundance of data, we cannot yet estimate when this process will be completed," Ekkehard Zimmer, hospital's commercial director said.
Healthcare Not to Be Targeted
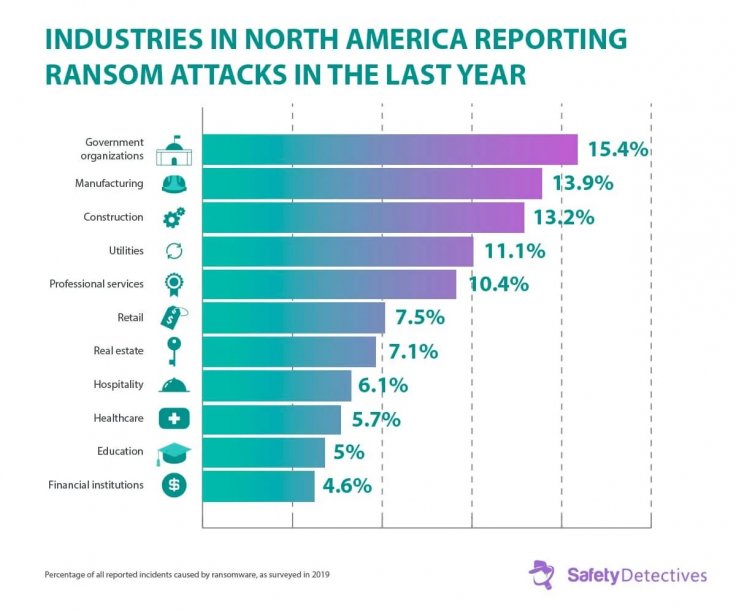
In the U.S. alone over 750 healthcare providers were targeted with ransomware attacks last year as per Emsisoft statistics. But with the ongoing Coronavirus pandemic, many hackers have stayed away from attacking the hospitals.
BleepingComputer reached out to many known ransomware attackers such as CLOP, DoppelPaymer, Maze, and Nefilim and they said they would not target healthcare facilities. However, such attacks do happen due to misconfiguration of the network. But they said that if they attack by mistake, a free decryption key would be provided.
However, the BSI once again warned the hospitals in the country to be aware of such threats to prevent any unfortunate incident in the future. The incident shows once again how seriously this danger must be taken. This is one of the reasons why the federal government has provided in the draft of the Hospital Future Act that "at least 15 percent of the funding requested must be used for measures to improve information security," Schonbohm said.









