The infamous "Lazarus Group," a gang of North Korean state-supported hackers behind some of the largest online money thefts of all time, is now cyberattacking key U.S. industries, including defense, energy and banks.
The cybercrime group's latest operation has been given the codename "Operation Sharpshooter" by cybersecurity firm, McAfee. This criminal operation, which has likely been going on for some 18 months, is also targeting the U.S. energy and telecommunications industry, oil and gas companies and the federal government.
McAfee revealed the Lazarus Group is attacking more than 100 targets in the U.S. and other Western countries. It said most of the U.S. targets are in Houston and New York City. International targets are government agencies and private firms located in London, Madrid, Tokyo, Tel Aviv and Hong Kong.
McAfee noted that cities in Russia and mainland China, which maintain good relations with North Korea, are not being attacked by the Lazarus Group.
McAfee said securing access to one of the main computer servers used by the Lazarus Group allowed it to watch the attacks unfold in real-time.
The Lazarus Group hackers "are very, very, very active. It's been nonstop," said Raj Samani, chief scientist at McAfee. He also said the attacks are highly sophisticated and perpetrated to access computer networks and intellectual property at specific companies.
McAfee confirmed the bulk of the group's attacks center on banks, utilities and oil and gas companies.
The cyberattacks took place even as North Korean dictator Kim Jong-un met with president Donald Trumpin Hanoi, Vietnam last week during their failed second summit.
Cybersecurity analysts noted with some cynicism that North Korea might have suspended testing its ballistic missiles, but has not called a halt to its criminal cyberattacks against other countries and international business firms. These attacks appear to have intensified.
"North Korea appears to be engaging in increasingly hostile cyber activities, including theft, website vandalism, and denial of service attacks," said McAfee in a report released in March 2018.
The Lazarus Group's focus on hacking banks and stealing their money is understandable: sanctions-hit North Korea is short of cash and needs to get its hands on as much money as it can to prevent its economy from collapsing. Its track record of thievery is astounding.
The Lazarus Group stole $12 million from the Banco del Austro in Ecuador and US$1 million from Vietnam's Tien Phong Bank in 2015. They've also stolen undisclosed sums from banks in Poland and Mexico.
Among its most successful capers is the 2018 attack on the Bangladesh Bank in which it stole $81 million. In 2017 the Lazarus Group stole $60 million from the Far Eastern International Bank of Taiwan.
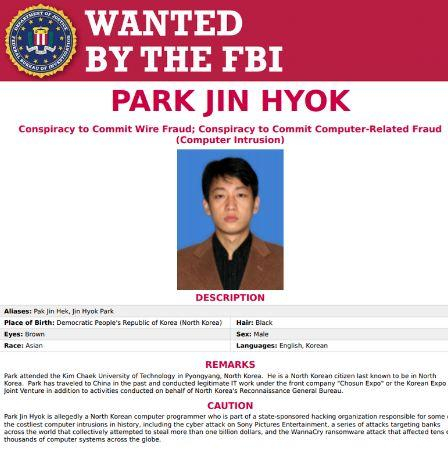
The group was also behind the 2014 attack on Sony Pictures where it attempted to extort money in exchange for the data it stole.
This article was first published in IBTimes US. Permission required for reproduction.









