A multinational cyber security and defence company Trend Micro stated in a recently published report that a group of cybercriminals has planted malicious JavaScript code to steal payment card details inside the e-commerce system used by Canada and US-based colleges and universities.
As per the report, which was released on Friday, May 3, the code was found in 201 online campus stores in both the countries that include America's 176 colleges and universities as well as 21 Canada based educational institutions.
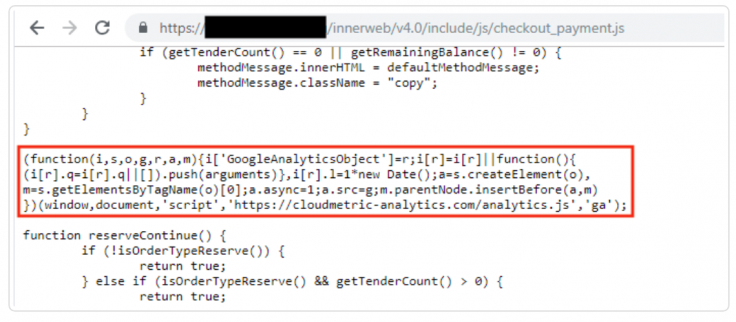
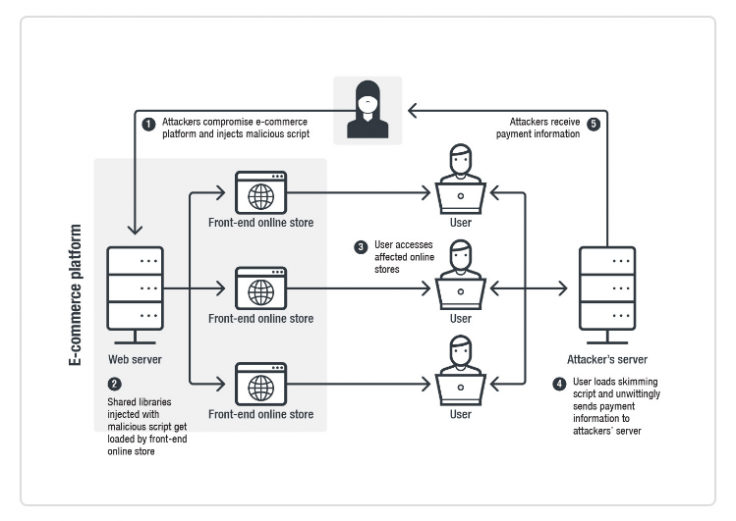
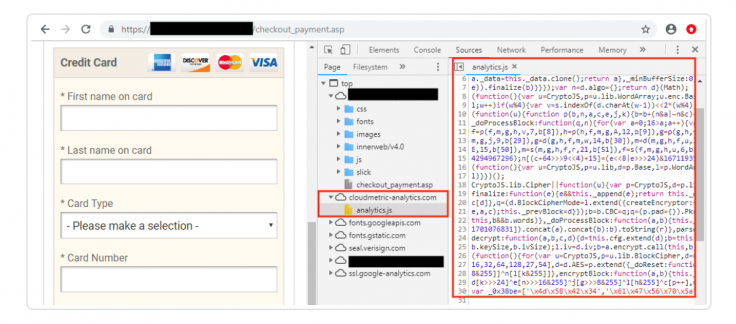
Trend Micro analysis team started detecting the notorious online credit card skimming attack, called as Magecart, against multiple campus store websites on April 14. Their findings showed that the hackers successfully place malicious JavaScript code on the checkout and payment pages of those online stores. This skimming script "can scrape credit card information, as well as personal details entered on the payment page," said the report.
The recorded payment card data can be uploaded to the servers of the hackers or can be sold on underground cybercrime platforms.
The report added that "After looking into this attack, we learned that the attackers compromised PrismWeb, which is an e-commerce platform designed for college stores by company PrismRBS, a subsidiary of Nebraska Book Company."
Trend Micro said the attackers hacked PrismRBS and modified the PrismWeb platform to add the JavaScript files which were loaded on all of the active PrismWeb deployments. The company stated that the script was active until April 26 but the amount of stolen payment information is still unknown.
However, after the IT security company, headquartered in Japan, notified the vendor about the malicious script, PrismRBS said in an official statement that they were informing all the colleges and engaging with an external IT forensic firm to investigate the incident.
"Our investigation is ongoing to determine the scope of the issue, including who and what information may have been impacted. Based on our review to date, we have determined that an unauthorized party was able to install malicious software designed to capture payment card information on some of our customers' e-commerce websites," it added.