An unsecured or poorly secured Wi-Fi connection has been one of the biggest cybersecurity risks that has led to billions of dollars in losses. Hence, businesses and even households are urged to use strong passwords and secure their connection with the latest encryption method. As for important works, many businesses store data on air-gapped computers that have never been connected to a network. But what if other components on a computer could be hacked to steal data? That's what a group of security researchers has done. By converting memory modules (RAM) into a temporary Wi-Fi card, they were able to steal data.
Air-gapped computers are considered almost impossible to hack without physical access. Such systems are used by government agencies and the military to store sensitive information with no access to the internet or any local network such as Bluetooth. But Mordechai Guri from the Ben-Gurion University of the Negev, Israel managed to hack such a computer using a novel method called AIR-FI.

How Does AIR-FI Hack Work?
Guri, who is the head of R&D at the university, has done numerous research projects that involve stealing information through novel methods from air-gapped computers. This way, a future attack could be prevented and won't surprise the security teams. His latest project was built around that but with a different technique. Instead of breaching an air-gapped computer what if the information could be stolen from the memory without even accessing it? It sounds too good to be true but they were able to achieve that.
Every electronic component generates electromagnetic waves when the electrical current passes through the chips. Wi-Fi signals also work the same way. When you power on a router, it generates a radio wave that is also a type of electromagnetic wave. Guri's idea was to plant a malicious code or malware in the air-gapped system that would manipulate the electrical current inside the chips on the RAM (Random Access Memory) sticks that stores data temporarily. By doing so, it would be able to generate electromagnetic of 2.4 GHz or 2,400 MHz similar to the Wi-Fi spectrum, according to the research paper.

However, if the memory module on the air-gapped computer is not near the 2,400 MHz frequency, the malware would allow overclocking or downclocking of the memory frequency through the BIOS/UEFI firmware. Nowadays, most DDR4 memory modules come with a minimum frequency of 1600 MHz and can range up to 5,000 MHz. But through UEFI/BIOS, it can be overclocked to 2,400 MHz or beyond to match the Wi-Fi spectrum (between 2,401 to 2,495 MHz or 2.4 GHz).
It should be noted that a DDR SDRAM module comes with 800 MHz up to 2,500 MHz. But due to the Double Data Rate (hence, DDR) nature, the speed is double.
By using his technique, Guri said he was able to pick up the wireless signal by any device with a WI-Fi antenna such as mobile phone, laptop, IoT devices, smartwatches amongst others. He was able to transfer data from the RAM sticks at speeds up to 100 bytes per second within a radius of few meters.
'One of the Easiest Attacks'
Guri told ZDNet that AIR-FI was one of the easiest techniques to pull off than other covert data exfiltration methods. With his technique, hackers won't even need to have administrative privileges or root access to run the exploit.
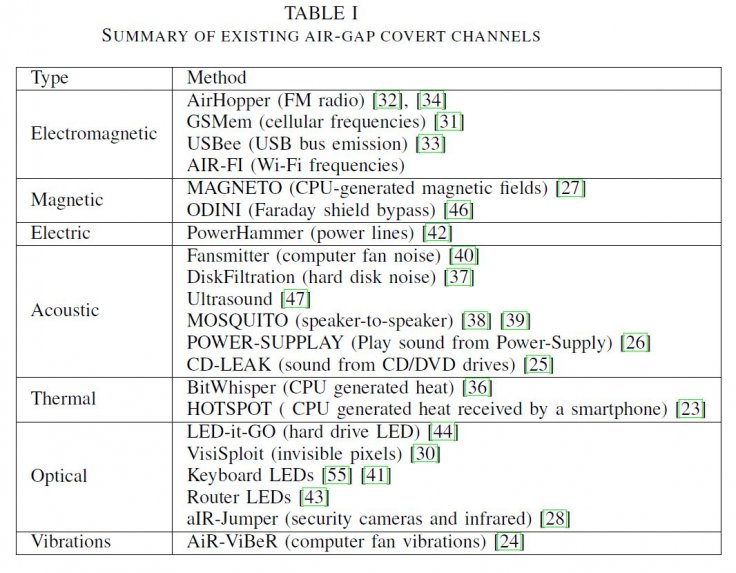
"AIR-FI can be initiated from an ordinary user-space process," Guri said, adding that the hack can be performed on any operating system or even from a virtual machine. Such covert data exfiltration methods are not new though. The Israeli researcher was earlier able to use different components of a computer to extract data without special privileges.
"Our results show that the covert channel can be effective at distances up to several meters from air-gapped computers. We achieved effective bit rates ranging from 1 to 100 bit/sec, depending on the type and mode of receiver used," Guri said.