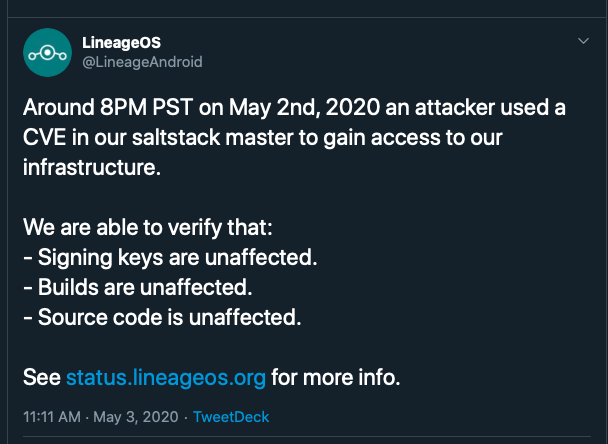
Hackers are exploiting some vulnerabilities in LineageOS, one of the biggest competitors to Google's Android operating systems. The vulnerabilities found in an open-source framework dubbed Salt have helped the attackers to invade and gain control of the LineageOS server to take down its official website. The hack has affected its mail servers, download mirrors, download portal, stats pages and a few more. Following the attack, the managers of the LineageOS official website have taken it down for thorough analysis.
LineageOS officials have explained that the operating system codes, however, remained untouched; hence there won't be any consequences for LineageOS users due to the hack. However, the Google Android substitute OS can't be downloaded until its website comes back to life. LineageOS is an Android-powered operating system used in a smartphone, tablet and set-top boxes. The OS was counted as a significant competitor to Google's Android version until a few years back and still counted as one of the best builds among rooted device users.
The LineageOS hack
The developers at LineageOS have reportedly mentioned two unpatched vulnerabilities in its servers which were behind the attack. According to the report, the vulnerabilities existed in the Salt installation of the website server. Salt is an integral part of the popular management framework SaltStack. The open-source management framework is widely popular in data centres and cloud servers for its capability to automate the process.
The discovery
The dangerous remote code execution (RCE) vulnerabilities were discovered by a bunch of researchers from cybersecurity solution provider F-Secure a few days back. In its analysis blog, F-Secure mentioned that any expert attacker could successfully create exploits using the vulnerabilities in just 24 hours. Interestingly, the LineageOS hack was executed just a couple of days after the vulnerabilities were discovered.
The vulnerabilities
The vulnerabilities CVE-2020-11651 and CVE-2020-11652 can together help an attacker to intrude into any Salt server left open on the internet without any authentication and take control of the server.
The hacking mayhem
According to reports from the Salt server owners, both the bugs were exploited by a few attackers for compromising website authentication and installing backdoors on their systems. They have also installed crypto mining software on a few compromised servers.
According to reports, there are over 6,000 Salt server left open on the internet, which can be compromised by using the vulnerabilities.
ZDNet has reported that cyber attackers are actively scanning for the Salt servers available on the internet and could launch a series of attacks targeting enterprise networks, cloud servers and data centres.
Following the attack on LineageOS, hackers compromised WordPress alternative blogging platform Ghost. The Ghost developers have confirmed the compromise targeting their backend infrastructure. The developers have also mentioned both the vulnerabilities used to take control of its Salt master server. They have said that the attackers have implanted crypto mining software in it.










