With movement restrictions and lockdowns due to the COVID-19 pandemic, millions of people have preferred to shop online during the holiday season. Cybercriminals, however, are taking advantage of that situation with scams and malware targeting online shoppers. Among those, an Amazon gift card scam has attracted the attention of cybersecurity researchers as it could not only cost you money but also make your device vulnerable to hacking.
Discovered by cybersecurity research firm Cybereason, the scam is targeted to people in Europe and the US. As many people are staying home, gift cards have become a popular tool to present to loved ones during Christmas. However, one such "too good to be true offer" is designed to serve Dridex banking trojan.
"Both cybercriminals and nation-state threat actors alike find and exploit trending circumstances in order to leverage a given situation to infect unsuspecting victims, such as the holiday season, the ongoing COVID-19 pandemic, or both of them combined," Daniel Frank, a cybersecurity researcher at Cybereason said in a blog post.

Dridex Malware
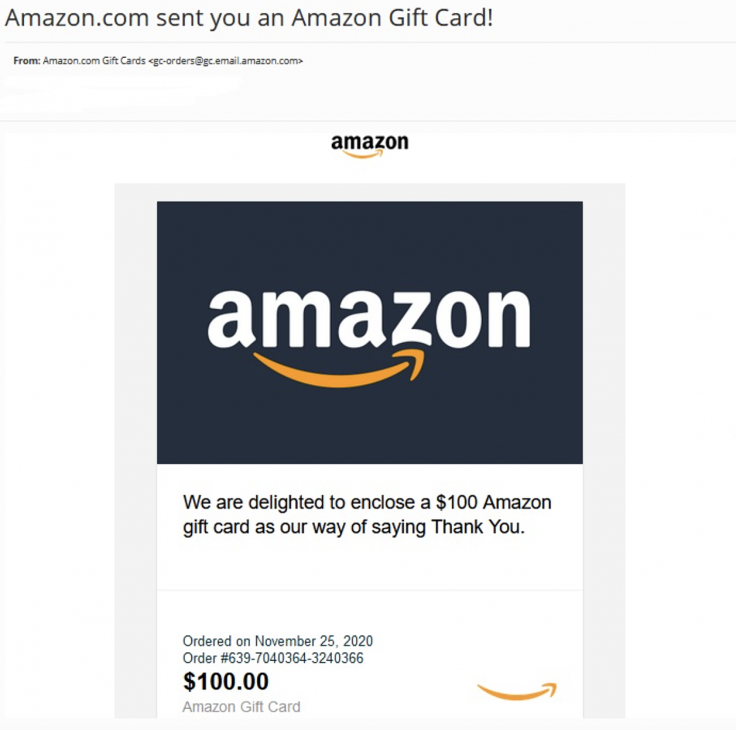
The malware is delivered by phishing attacks through a spoofed email that reads: "We are delighted to enclose a $100 Amazon gift card as our way of saying Thank You." The email also contains Amazon order date and number. However, the email comes with a malicious word document or screensaver file attached. After downloading the attachment, the users are redirected to Amazon's legitimate webpage, "gaining more credibility with the victim."
Once the user opens the document, it prompts to run a malicious macro. After enabling the macro, it shows a fake error message "Word experienced an error trying to open the file". But in reality, a Windows PowerShell script runs in the background to serve the Dridex malware.
Apart from spoofed emails, hackers are also using a second delivery method involving screensaver files (with .scr extension). Using SCR to infect devices has gained popularity amongst hackers as it helps them bypass email spam filters. Once downloaded, the SCR file extracts the malware payload, a technique associated with Dridex malware that is used to gather banking credentials.
"The current campaign that targets consumers who are falsely informed they have received an Amazon gift card and infects the target with three similar yet unique techniques; similar in terms of luring the victim into clicking the file, and different in terms of the execution flow," Frank added.
Amazon Confirms Attacks
Following Cybereason's investigation, Amazon also acknowledged the presence of the scam and warned users to verify such gift cards with friends and families who gave them. "Fraudsters use many methods to conduct scams, including requesting gift cards from well-known brands for payment. We want to make sure our customers are aware of scams that may request payment using Amazon Gift Cards," the online retailer said.
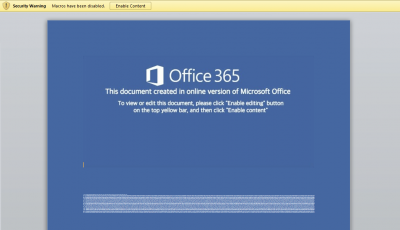

If you receive such an email, you should delete it immediately without opening it. However, if you open such an email, do not download any attachments and enable the macro. Microsoft Office disables macros by default so it would not run automatically.
"Post-infection, the implementation of the payload deployment on the machine is often multi-staged and highly evasive. This current Dridex campaign introduced three different attack vectors. In case one fails to work perhaps the other will, thus creating a backup mechanism not only for their C2 servers but also for completing the infection process itself," Frank explained.









