Joker Android malware which is also known as Bread have been detected and removed by Google's Play Protect from the Play Store since the tech giant found the vulnerability in 2017. Earlier, the researchers from CSIS Security Group security said that they found 24 Play Store apps with over 472,000 downloads in total during September 2019.
The Singapore-based cybersecurity company, Group-IB revealed on Friday that they have detected a database containing over 460,000 payment card records uploaded to one of the most popular darknet card shops on February 5.
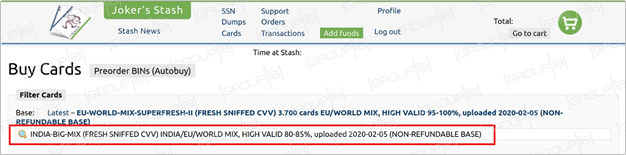
The darknet cardshop

As per the security company, they noticed that more than 98 percent of these leaked records were from the biggest Indian banks and understood that the underground market value of the database is estimated at more than $4.2 million. Even though the source of the batch is currently unknown, after discovering the issues, Group-IB has immediately informed the Indian Computer Emergency Response Team (CERT-In) about the sale of the payment records, so they could take necessary steps.
As per the experts, on February 5, a new database under the name "INDIA-BIG-MIX" (full name: [CC] INDIA-BIG-MIX (FRESH SNIFFED CVV) INDIA/EU/WORLD MIX, HIGH VALID 80-85%, uploaded 2020-02-05 (NON-REFUNDABLE BASE) went on sale on the Joker's Stash, which is one of the most popular underground card shops.
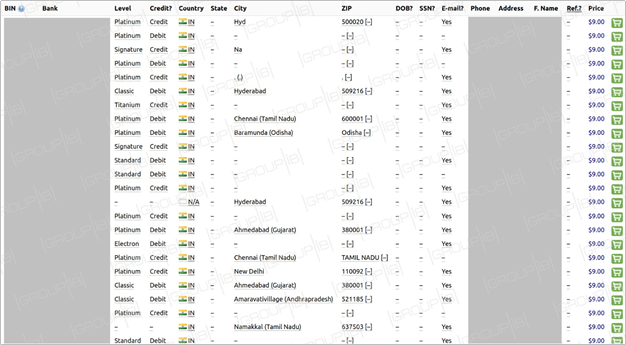
The leaked database
As per Group-IB Threat Intelligence team, the database, comprising 461,976 payment records, in particular, exposed card numbers, expiration dates, CVV/CVC codes and, in this case, some additional information such as cardholders' full name, as well as their emails, phone numbers and addresses. All the cards from the database are being sold for $9 for piece, with the total underground market value of all the batch standing at $4,157,784. As of morning on February 6, 16 cards were sold out.
The company stated that this is the only big sale of Indian cards' CC data detected for the past 12 months since in the previous India case, card dumps — the information contained in the card magnetic stripe — were put up for sale. What distinguishes the new database from its predecessor is the fact that the cards were likely compromised online, this assumption is supported by the set of data offered for sale.
Dmitry Shestakov, the head of Group-IB сybercrime research unit said that:
This is the second major leak of cards relating to Indian banks detected by Group-IB Threat Intelligence team in the past several month. In the current case, we are dealing with so-called fullz — they have info on card number, expiration date, CVV/CVC, cardholder name as well as some extra personal info. Such type of data is likely to have been compromised online — with the use of phishing, malware, or JS-sniffers — while in the previous case, we dealt with card dumps (the information contained in the card magnetic stripe), which can be stolen through the compromise of offline POS terminals, for example. We have shared all the information discovered with our colleagues from CERT-In.
However, while explaining the scenario the security company mentioned that one of the reasons behind the carding market boosting were the activities of JS-sniffers, which enable their operators to steal payment card data from eCommerce websites.
As per Group-IB, "This threat can hardly be underestimated: the APAC region has recently seen its first arrest of JS-sniffers' operators, who stole payment card data with the help of GetBilling JS-sniffer family. The arrest came as a result of a joint operation of INTERPOL, Group-IB and Indonesian police."









