OHS, a major hospital chain with over 400 facilities in the U.S., the U.K. and Puerto Rico has been forced to shut down its systems due to a cyber attack. According to reports, employees in Washington DC, Texas, Florida, Arizona and California facilities have no access to the computers and phone system due to the ongoing cyber attack.
Universal Health Service (UHS), which is a Fortune 500 healthcare provider with over 90,000 employees, offers healthcare service to more than 3.5 million patients every year. While UHS has admitted to an ongoing "IT security issue", it said in a statement that no patient or employee data has been "accessed, copied or misused."
"Our facilities are using their established back-up processes including offline documentation methods. Patient care continues to be delivered safely and effectively," UHS said in a statement.

Chaos at UHS hospitals
With heavy reliance on the online system, most of the patient record is now digital. As per some employee accounts on social media posts, doctors and health workers are not able to access patients' records including EKGs, other radiology, lab reports and medication lists. Now, they are relying on paper backup to check for patient records.
"We have no access to anything computer-based," said an individual who identified as an employee of the organization in a Reddit post, adding that the attack happened during the night September 27. A Texas hospital clinician part of UHS told the Associated Press that as they are forced to rely on paper backups and emergency room wait has increased from 45 minutes to six hours with no access to patient history or records.
The other problem is that the ongoing Coronavirus pandemic. With no access to patient data, healthcare workers are concerned about how to identify if a patient is suffering from COVID-19. A Washington facility clinician said that there was a lot of anxiety among staff during the shift.

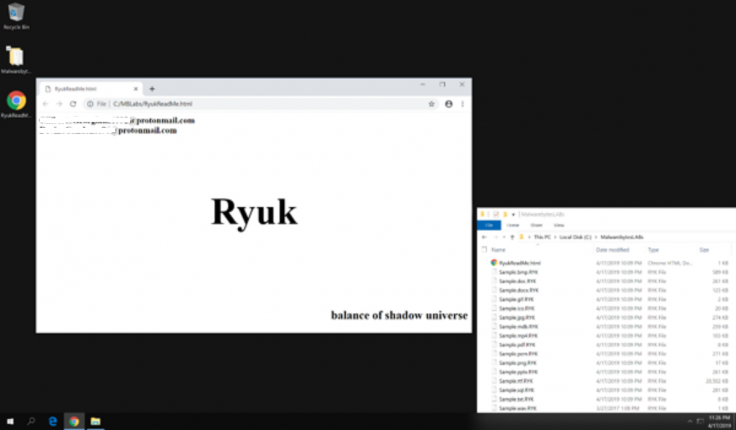
Ryuk Ransomware
While UHS didn't mention the nature of the attack, supposed employee accounts suggest a ransomware attack. The hard drives showed a sudden spark in activity while antivirus softwares were disabled automatically. As soon as the attack was detected, all remaining systems were shut down to avoid further encryption of files.
"When the attack happened multiple antivirus programs were disabled by the attack and hard drives just lit up with activity. After 1 min or so of this the computers logged out and shutdown. When you try to power back on the computers they automatically just shut down," said the employee.
A UHS employee told BleepingComputer that the files were being renamed with the ".ryk" extension that is used by Ryuk ransomware. Another claimed that one of the computers display changed to show a note "Shadow of the Universe" that is consistent with previously identified Ryuk ransomware attacks.
Andrew Thompson from Advanced Intel, a cybersecurity research firm, said in a tweet that the it was likely launched through a phishing attack. Another cybersecurity expert from Advanced Intel said that the company's Andariel platform detected Emotet and TrickBot Trojans targeting UHS network as recently as September 2020.
The Emotet trojan spreads via phishing emails with malicious attachments and then installs the malware on the system when clicked on it. Emotet then installs TrickBot which in turn creates a reverse shell to give the hackers access to the network with admin privileges. The attackers then plant Ryuk ransomware that encrypts data on the infected network using PowerShell Empire, as per experts.
Russian Actors Behind the Attack?
The Ryuk ransomware attack has previously been associated with Russian hackers. As per a report from January 2019, a Russian hacker group named Wizard Spider had been targeting large enterprises with Ryuk ransomware. Since the Ryuk malware emerged in August 2018, hackers have netted over $3 million across 52 attacks.
Of late, there has been an increase in ransomware attacks on healthcare networks. Over 700 hospitals in the U.S. alone were targeted in 2019. Recently, a patient died due to an indirect result of a ransomware attack in a German hospital. As the hospital was unable to access patient records, it had to reroute one of the patients who needed urgent care to a distant medical center but she died shortly. She was the first-ever reported casualty of a cyberattack.









