
Researchers at a software company Proofpoint disclosed that Chinese state-sponsored hacking group called APT10 is suspected to be the likely culprit behind the cyber campaign targeting US-based companies.
Proofpoint revealed that APT10, also known as Stone Panda, MenuPass and Red Apollo and believed to work for the country's Ministry of State Security, is likely to have taken up this task between July 19 and 25. Several spear-phishing emails, identified to be targeting three US companies in the utility sector, trying to impersonate a US-based engineering licensing board with emails. They originated from "what appears to be an actor-controlled domain, nceess[.]com. Nceess[.]com, which is believed to be an impersonation of a domain owned by the US National Council of Examiners for Engineering and Surveying."
The report mentioned that these emails contained a malicious Microsoft Word attachment that uses macros to install and run malware that researchers have dubbed "LookBack." As per the experts, this malware "consists of a remote access Trojan (RAT) module and a proxy mechanism used for command and control (C&C) communication."
"This may be the work of a state-sponsored APT actor based on overlaps with historical campaigns and macros utilized. The utilization of this distinct delivery methodology coupled with unique LookBack malware highlights the continuing threats posed by sophisticated adversaries to utility systems and critical infrastructure providers," revealed the researchers at Proofpoint.
In addition, it showed an image of the National Council of Examiners for Engineering and Surveying (NCEES)-themed phishing email. The report showed that the spare-phishing campaign targeted company employees with emails claiming to be from NCEES while purporting to be delivering professional examination results, utilizing the NCEES logo. But actually were delivering "malicious" Microsoft Word attachments.
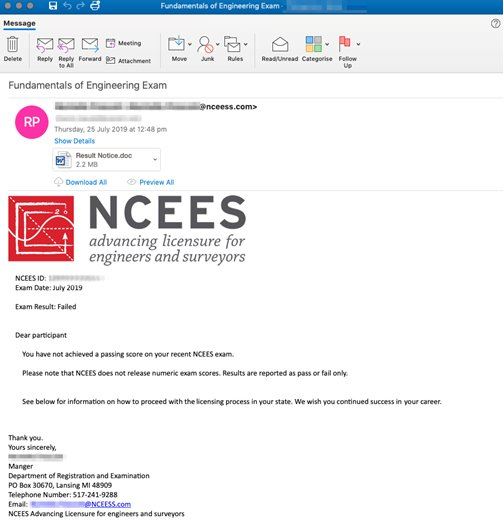
The researchers, Michael Raggi and Dennis Schwarz explained that "the email sender address and reply-to fields contained the impersonation domain nceess[.]com. Like the phishing domain, the email bodies impersonated member ID numbers and the signature block of a fictitious employee at NCEES."
They also found that the phishing messages contained an attached Microsoft Word document that uses VBA macros to install LookBack malware and once the attachment is executed, the malicious VBA macro drops Privacy Enhanced Mail (PEM) files onto the host computer which then provide the malware with the command and control framework needed to access data on the system.
While explaining the LookBack malware, they mentioned that it is a remote access Trojan written in C++ that relies on a proxy communication tool to relay data from the infected host to a command and control IP.
This malware includes an "enumeration of services; viewing of process, system, and file data; deleting files; executing commands; taking screenshots; moving and clicking the mouse; rebooting the machine and deleting itself from an infected host."
A joint report published by Recorded Future and Rapid7 accused APT10, which has been active since at least 2009, for infiltrating one of the largest cloud service providers in Europe, Visma.
UK's National Cyber Security Centre (NCSC) added that after the identification of APT10, the authorities found that it has been targeting healthcare, defence, aerospace, government, heavy industry and mining.









