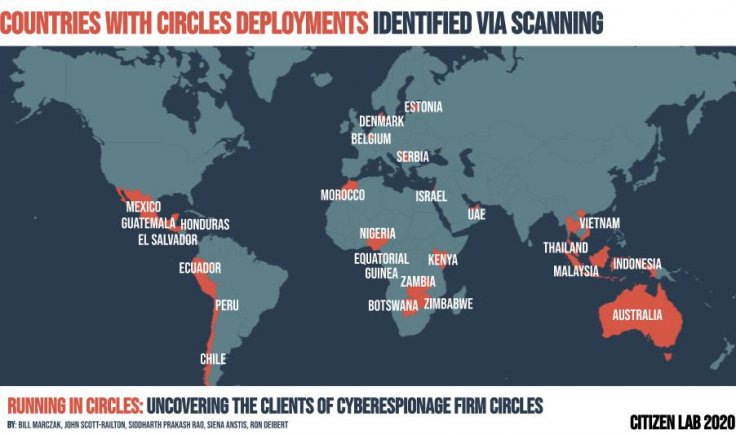
As technologies have advanced, governments have either found new ways of surveillance on its citizens or have broadened the scope of surveillance. Now, new evidence suggests that at least 25 countries in Europe, Asia, Africa and the Middle East apart from Australia have acquired technology that helps in intercepting communications and even remote location tracking of phones beyond its borders.
The stunning surveillance scheme was uncovered by the Citizen Lab, an online rights watchdog based in Toronto, Canada. In its report, published on December 1, it claimed that the phone surveillance technology was purchased from an Israeli company named Circles which later merged with NSO, a government malware vendor. NSO supplies governments across the world with SS7 phone tracking service. While the SS7 is a network protocol used for roaming, it can be exploited for surveillance.

According to the report, many countries with a history of human rights abuse might be purchasing the technology through which "you can track any phone number from any country and anywhere in the world," a source told Vice.
"Many of the government clients described above who appear to have acquired and/or deployed Circles technology have a dismal record of abuses of human rights and technical surveillance capabilities. Many lack public transparency and accountability, and have minimal or no independent oversight over the activities of their security agencies," Citizen Lab said in the report.
SS7 and Surveillance
SS7 or Signaling System No.7 is used by carriers to route calls to a partner network during roaming on 2G and 3G networks. However, its weakness allows hackers to send commands to a phone, indicating that the user is in roaming and track the location while also intercepting voice calls and SMS. Apart from that, Circles' PixCell technology can also intercept wireless and internet communications.
Citizen Lab identified Circles' customers by scanning servers for unique digital fingerprints. Using the method, the researchers identified where the tool was deployed. According to the report, it was able to extrapolate data from multiple data points and a web domain linked to Circles business.
Using the tool, UAE carried out surveillance on the Emir of Qatar and the Lebanon Prime Minister while also targeting human rights activist Ahmed Mansoor, Forbes reported. Circles' parent company NSO is notorious for its spyware tools. NSO is currently facing a lawsuit from Facebook for targeting 1,400 WhatsApp accounts through Android and iOS spyware. Mexico also used NSO's Pegasus spyware to track reporters and human rights activists.
'Predetermined Agenda'
NSO, however, criticized Citizen Lab and accused it of having a predetermined agenda. The company said that Circles' technology is used for search and rescue operations besides tactical geolocation technology. "We cannot comment on a report we have not seen. Given Citizen Lab's track record, we imagine this will once again be based on inaccurate assumptions and without a full command of the facts. As ever, we find ourselves being asked to comment on an unpublished report from an organization with a predetermined agenda," NSO said in a statement.
NSO and Circles aren't the only companies to develop spyware tools. Apart from government-developed tools, private companies such as Intellexa, Verint, 1rstWAP and Ability Inc among others offer similar services to governments. While most of the tools have been developed to aid the intelligence community, it is often used to silence dissent and keep track of political opponents and human rights activists.









